Releases: ory/kratos
v1.3.1
This release adds the ability to verify Android passkeys.
Code Generation
- Pin v1.3.1 release commit (36e624c)
Features
-
Support android webauthn origins (b11d76e):
This patch adds the ability to verify Android APK origins used during WebAuthn/Passkey exchange.
Upgrades go-webauthn and includes fixes for Go 1.23 and workarounds for Swagger.
Changelog
Artifacts can be verified with cosign using this public key.
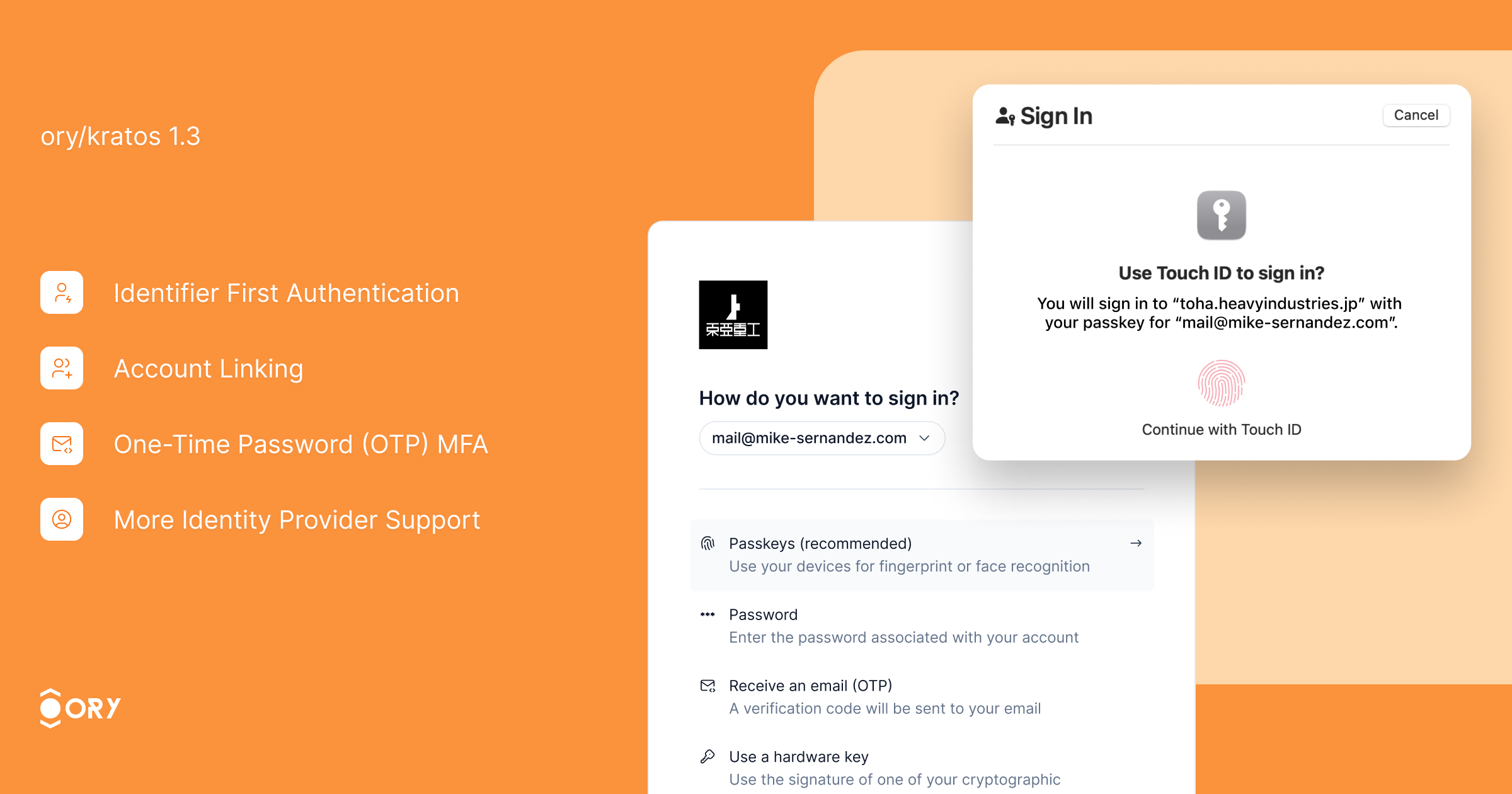
v1.3.0
We are thrilled to announce the release of Ory Kratos v1.3.0! This release includes significant updates, enhancements, and fixes to improve your experience with Ory Kratos.
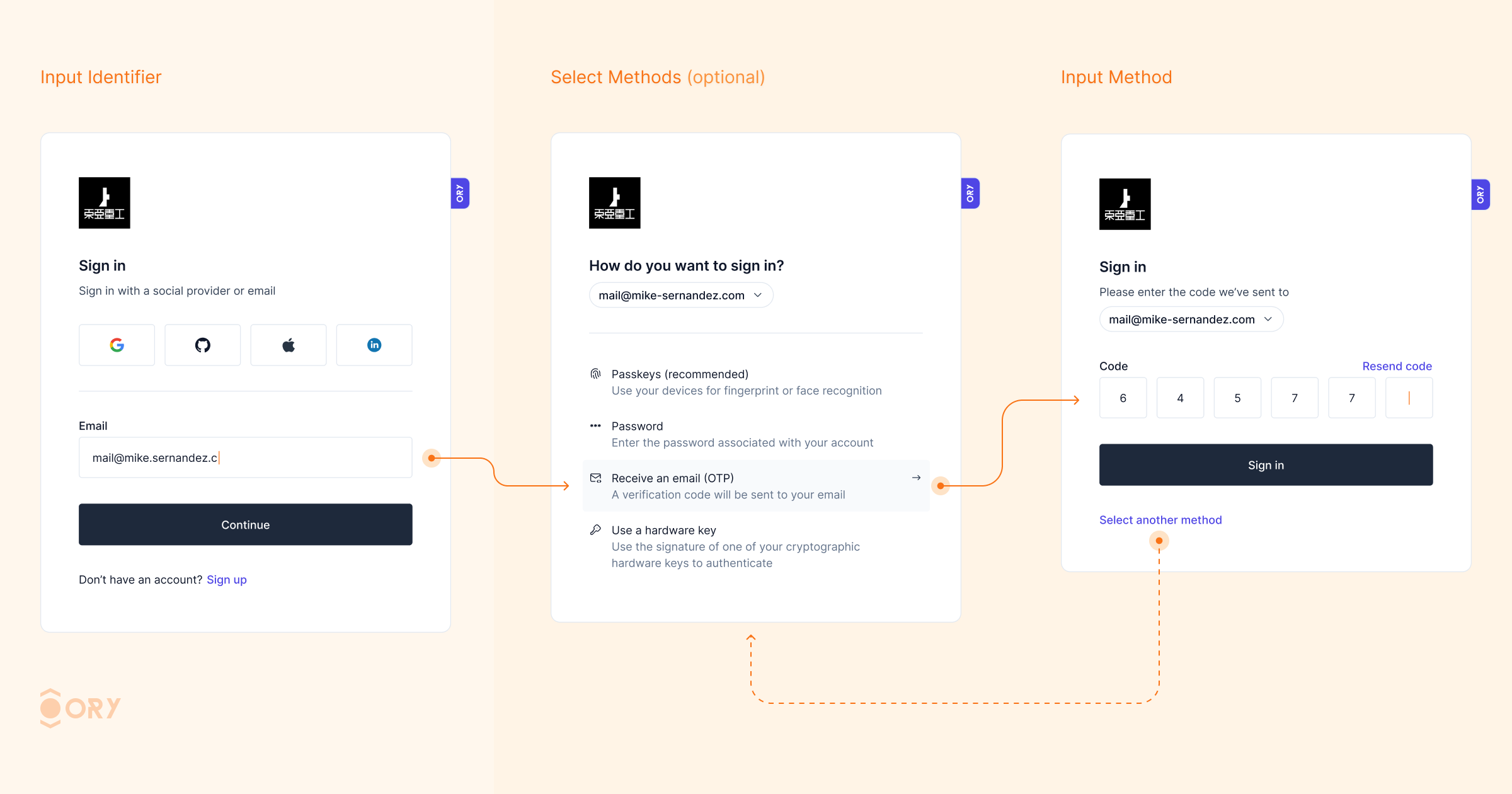
Enhance your sign-in experience with Identifier First Authentication. This feature allows users to first identify themselves (e.g., by providing their email or username) and then proceed with the chosen authentication method, whether it be OTP code, passkeys, passwords, or social login. By streamlining the sign-in process, users can select the authentication method that best suits their needs, reducing friction and enhancing security. Identifier First Authentication improves user flow and reduces the likelihood of errors, resulting in a more user-friendly and efficient login experience.
The UI for OpenID Connect (OIDC) account linking has been improved to provide better user guidance and error messages during the linking process. As a result, account linking error rates have dropped significantly, making it easier for users to link multiple identities (e.g., social login and email-based accounts) to the same profile. This improvement enhances user convenience, reduces support inquiries, and offers a seamless multi-account experience.
You can now use Salesforce as an identity provider, expanding the range of supported identity providers. This integration allows organizations already using Salesforce for identity management to leverage their existing infrastructure, simplifying user management and enhancing the authentication experience.
Social sign-in has been enhanced with better detection and handling of double-submit issues, especially for platforms like Facebook and Apple mobile login. These changes make the social login process more reliable, reducing errors and improving the user experience. Additionally, Ory Kratos now supports social providers in credential discovery, offering more flexibility during sign-up and sign-in flows.
One-Time Password (OTP) MFA has been improved with more robust handling of code-based authentication. The enhancements ensure a smoother flow when using OTP for multi-factor authentication (MFA), providing clearer guidance to users and improving fallback mechanisms. These updates help to prevent users from being locked out due to misconfigurations or errors during the MFA process, increasing security without compromising user convenience.
-
Deprecated
viaParameter for SMS 2FA: Theviaparameter is now deprecated when performing SMS 2FA. If not included, users will see all their phone/email addresses to perform the flow. This parameter will be removed in a future version. Ensure your identity schema has the appropriate code configuration for passwordless or 2FA login. -
Endpoint Change: The
/admin/session/.../extendendpoint will now return 204 No Content for new Ory Network projects. Returning 200 with the session body will be deprecated in future versions. -
SDK Enhancements: Added new methods and support for additional actions in the SDK, improving integration capabilities.
-
Password Migration Hook: Added a password migration hook to facilitate migrating passwords where the hash is unavailable, easing the transition to Ory Kratos.
-
Partially Failing Batch Inserts: When batch-inserting multiple identities, conflicts or validation errors of a subset of identities in the batch still allow the rest of the identities to be inserted. The returned JSON contains the error details that led to the failure.
-
Security Fixes: Fixed a security vulnerability where the
codemethod did not respect thehighest_availablesetting. Refer to the security advisory for more details. -
Session Extension Issues: Fixed issues related to session extension to prevent long response times on
/session/whoamiwhen extending sessions simultaneously. -
OIDC and Social Sign-In: Fixed UI and error handling for OpenID Connect and social sign-in flows, improving the overall experience.
-
Credential Identifier Handling: Corrected handling of code credential identifiers, ensuring proper detection of phone numbers and correct functioning of SMS/email MFA.
-
Concurrent Updates for Webhooks: Fixed concurrent map update issues for webhook headers, improving webhook reliability.
-
Passwordless & 2FA Login: Before upgrading, ensure your identity schema has the appropriate code configuration when using the code method for passwordless or 2FA login.
-
Code Method for 2FA: If you use the code method for 2FA or 1FA login but haven't configured the code identifier, set
selfservice.methods.code.config.missing_credential_fallback_enabledtotrueto avoid user lockouts.
We hope you enjoy the new features and improvements in Ory Kratos v1.3.0. Please remember to leave a GitHub star and check out our other open-source projects. Your feedback is valuable to us, so join the Ory community and help us shape the future of identity management.
Breaking Changes
When using two-step registration, it was previously possible to send method=profile:back to get to the previous screen. This feature was not documented in the SDK API yet. Going forward, please instead use screen=previous.
Please note that the via parameter is deprecated when performing SMS 2FA. It will be removed in a future version. If the parameter is not included in the request, the user will see all their phone/email addresses from which to perform the flow.
Before upgrading, ensure that your identity schema has the appropriate code configuration when using the code method for passwordless or 2fa login.
If you are using the code method for 2FA login already, or you are using it for 1FA login but have not yet configured the code identifier, set selfservice.methods.code.config.missing_credential_fallback_enabled to true to prevent users from being locked out.
Please note that the via parameter is deprecated when performing SMS 2FA. It will be removed in a future version. If the parameter is not included in the request, the user will see all their phone/email addresses from which to perform the flow.
Before upgrading, ensure that your identity schema has the appropriate code configuration when using the code method for passwordless or 2fa login.
If you are using the code method for 2FA login already, or you are using it for 1FA login but have not yet configured the code identifier, set selfservice.methods.code.config.missing_credential_fallback_enabled to true to prevent users from being locked out.
Going forward, the /admin/session/.../extend endpoint will return 204 no content for new Ory Network projects. We will deprecate returning 200 + session body in the future.
Bug Fixes
-
Add continue with only for json browser requests (#4002) (e0a4010)
-
Add fallback to providerLabel (#3999) (d26f204):
This adds a fallback to the provider label when trying to register a duplicate identifier with an oidc.
Current error message:
Signing in will link your account to "[email protected]" at provider "". If you do not wish to link that account, please start a new login flow.The label represents an optional label for the UI, but in my case it's always empty. I suggest we fallback to the provider when the label is not present. In case the label is present, the behaviour won't change.
Fallback to provider:
Signing in will link your account to "[email protected]" at provider "google". If you do not wish to link that account, please start a new login flow. -
Add missing JS triggers (7597bc6)
-
Do not populate
id_firstfirst step for account linking flows (#4074) (6ab2637) -
Emit SelfServiceMethodUsed in SettingsSucceeded event (#4056) (76af303)
-
Include duplicate credentials in account linking message (#4079) (122b63d)
-
Incorre...
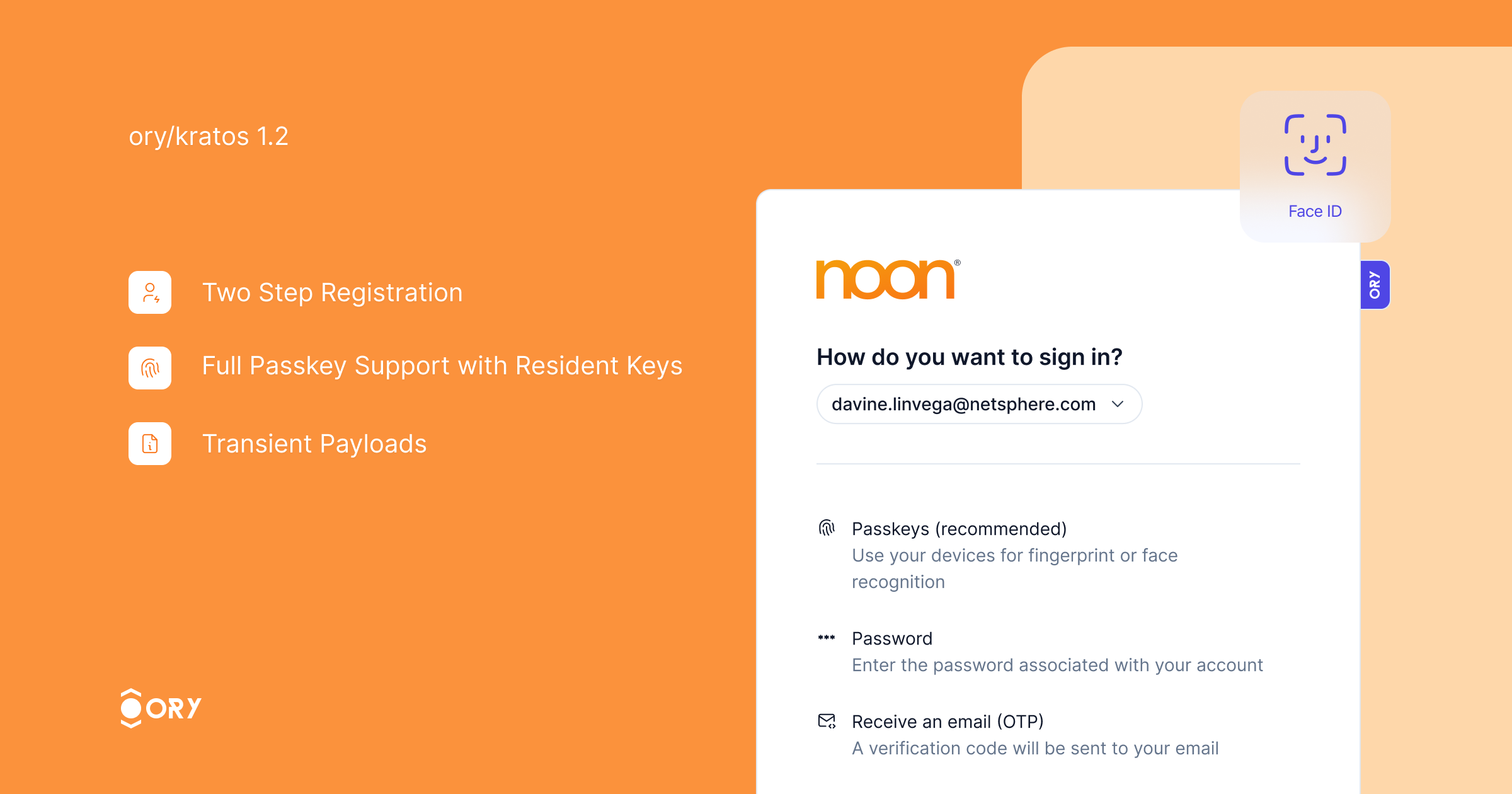
v1.2.0
Ory Kratos v1.2 is the most complete, scalable, and secure open-source identity server available. We are thrilled to announce its release!
This release introduces two major features: two-step registration and full PassKey with resident key support.
Passkeys provide a secure and convenient authentication method, eliminating the need for passwords while ensuring strong security. With this release, we have added support for resident keys, enabling offline authentication. Credential discovery allows users to link existing passkeys to their Ory account seamlessly.
passkeys.webm
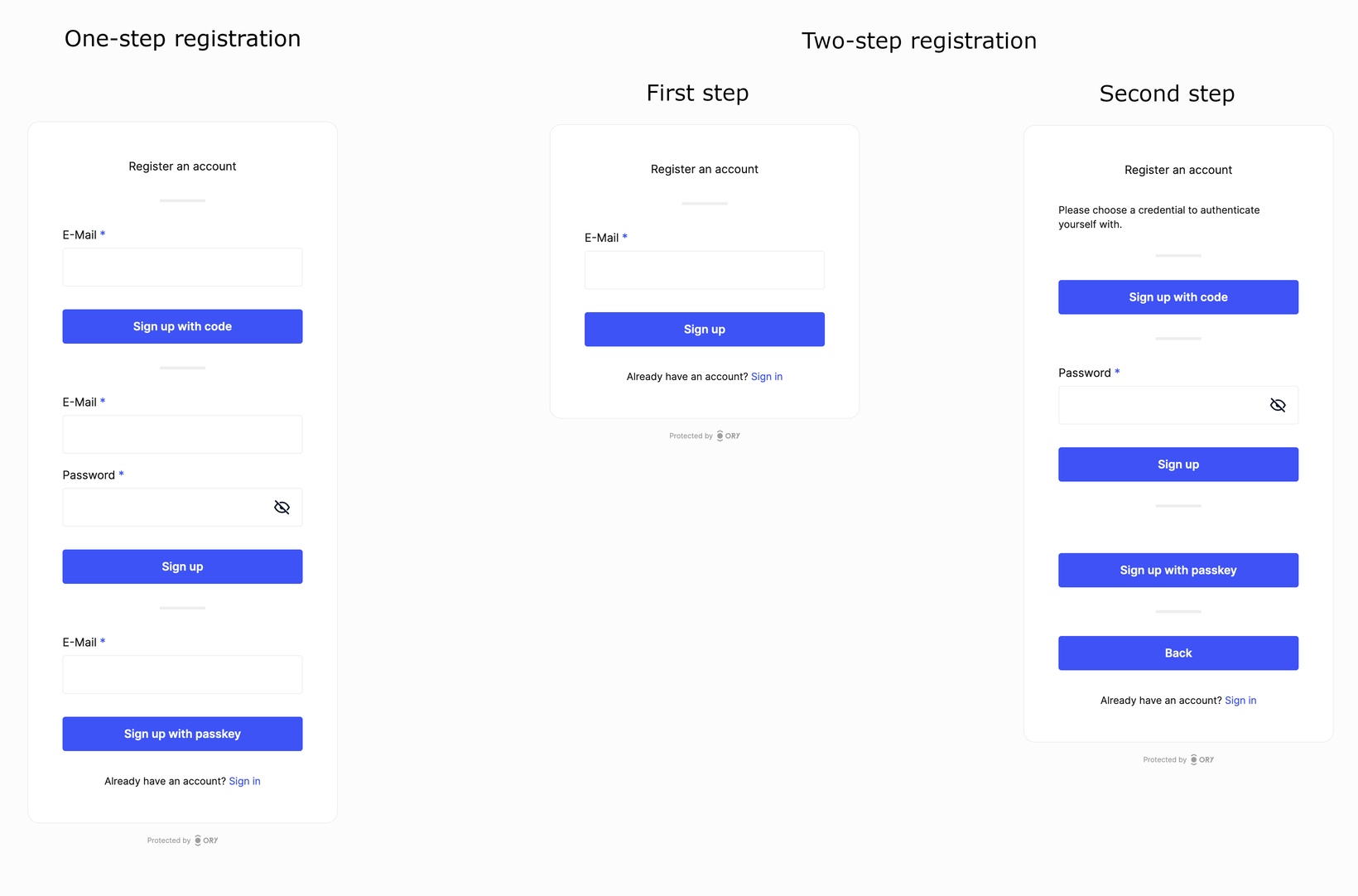
Two-step registration improves the user experience by dividing the registration process into two steps. Users first enter their identity traits, and then choose a credential method for authentication, resulting in a streamlined process. This feature is especially useful when enabling multiple authentication strategies, as it eliminates the need to repeat identity traits for each strategy.
The 107 commits since v1.1 include several improvements:
- Webhooks now carry session information if available.
- Transient Payloads are now available across all self-service flows.
- Sign in with Twitter is now available.
- Sign in with LinkedIn now includes an additional v2 provider compatible with LinkedIn's new SSO API.
- Two-Step Registration: An improved registration experience that separates entering profile information from choosing authentication methods.
- User Credentials Meta-Information can now be included on the list endpoint.
- Social Sign-In is now resilient to double-submit issues common with Facebook and Apple mobile login.
Two-Step Registration Enabled by Default: This is now the default setting. To disable, set selfservice.flows.registration.enable_legacy_one_step to true.
- Improved account linking and credential discovery during sign-up.
- The
return_toparameter is now respected in OIDC API flows. - Adjustments to database indices.
- Enhanced error messages for security violations.
- Improved SDK types.
- The
verificationandverification_uihooks are now available in the login flow. - Webhooks now contain the correct identity state in the after-verification hook chain.
We are doing this survey to find out how we can support self-hosted Ory users better. We strive to provide you with the best product and service possible and your feedback will help us understand what we're doing well and where we can improve to better meet your needs. We truly value your opinion and thank you in advance for taking the time to share your thoughts with us!
Fill out the survey now!
Breaking Changes
This feature enables two-step registration per default. Two-step registration is a significantly improved sign up flow and recommended when using more than one sign up methods. To disable two-step registration, set selfservice.flows.registration.enable_legacy_one_step to true. This value defaults to false.
Bug Fixes
-
Add login succeeded event to post registration hook (#3739) (b685fa5)
-
Add missing env vars to set up guide (#3855) (da90502):
Closes #3828
-
Add missing indexes and remove unused index (6d7372e)
-
Add missing indexes and remove unused index (#3756) (c905f02)
-
Allow updating just the verified_at timestamp of addresses (#3880) (696cc1b)
-
Always issue session last (#3876) (e942507):
In post persist hooks, the session issuance hook always needs
to come last. This fixes the getHooks function to ensure this. -
Db index and duplicate credentials error (#3896) (9f34a21):
- fix: don't return password cred type if empty
- fix: better index for config.user_handle on identity_credentials
-
Do not require method to be passkey in settings schema (#3862) (660f330)
-
Execute verification & verification_ui properly in login flows (#3847) (5aad1c1)
-
Ignore decrypt errors in WithDeclassifiedCredentials (#3731) (8f5192f)
-
Include all creds in duplicate credential err (#3881) (e06c241)
-
Make sure emails can still be sent with SMS enabled (#3795) (7c68c5a)
-
oidc: Grace period for continuity container on oidc callbacks (#3915) (1a9a096)
-
Respect return_to in OIDC API flow error case (#3893) (e8f1bcb):
- fix: respect return_to in OIDC API flow error case
This fix ensures that we redirect the user to the return_to URL
when an error occurs during the OIDC login for native flows.Native flows are initialized through the API, and the browser
URL is retrieved from a 422 response after a POST to submit the
login flow. Successful OIDC flows already returned thecodeto
thereturn_toURL. Now, unsuccessful flows return theflowwith
the current flow ID (which might have changed), so that the caller
can retrieve the full flow and act accordingly.- fix: ignore trivvy CVE report
Bump in distroless is still open
-
sdk: Expand identity in session extension ([#3843](https://g...
v1.1.0
Ory Kratos v1.1 is the most complete, most scalable, and most secure open-source identity server on the planet, and we are thrilled to announce its release! This release comes with over 270 commits and an incredible amount of new features and capabilities!
Don't forget to leave a GitHub star and check out our other open source projects while you're here :)
- Phone Verification & 2FA with SMS: Enhance convenient security with phone verification and two-factor authentication (2FA) via SMS, integrating easily with SMS gateways like Twilio. This feature not only adds a convenient layer of security but also offers a straightforward method for user verification, increasing your trust in user accounts.
- Translations & Internationalization: Ory Kratos now supports multiple languages, making it accessible to a global audience. This improvement enhances the user experience by providing a localized interface, ensuring users interact with the system in their preferred language.
- Native Support for Sign in with Google and Apple on Android/iOS: Get more sign-ups with native support for "Sign in with Google" and "Sign in with Apple" on mobile platforms. Great user experience matters!
- Account Linking: Simplify user management with new features that facilitate account linking. If a user registers with a password and later signs in with a social account sharing the same email, new screens make account linking straightforward, enhancing user convenience and reducing support inquiries.
- Passwordless "Magic Code": Introduce a passwordless login method with "Magic Code," which sends a one-time code to the user's email for sign-up and login. This method can also serve as a fallback when users forget their password or their social login is unavailable, streamlining the login process and improving user accessibility.
- Session to JWT Conversion: Convert an Ory Session Cookie or Ory Session Token into a JSON Web Token (JWT), providing more flexibility in handling sessions and integrating with other systems. This feature allows for seamless authentication and authorization processes across different platforms and services.
Note: To ensure a seamless upgrade experience with minimal impact, some of these features are gated behind the feature_flags config parameter, allowing controlled deployment and testing.
- Better reliability when sending out emails across different providers.
- Streamlining the HTTP API and improving related SDK methods.
- Better performance when calling the whoami API endpoint, updating identities, and listing identities.
- The performance of listing identities has significantly improved with the introduction of keyset pagination. Page pagination is still available but will be fully deprecated soon.
- Ability to list multiple identities in a batch call.
- Passkeys and WebAuthn now support multiple origins, useful when working with subdomains.
- The logout flow now redirects the user back to the
return_toparameter set in the API call. - When updating their settings, the user was sometimes incorrectly asked to confirm the changes by providing their password. This issue has now been fixed.
- When signing up with an account that already exists, the user will be shown a hint helping them sign in to their existing account.
- CORS configuration can now be hot-reloaded.
- The integration with Ory OAuth2 / Ory Hydra has improved for logout, login session management, verification, and recovery flows.
- A new passwordless method has been added: "Magic code". It sends a one-time code to the user's email during sign-up and log-in. This method can additionally be used as a fallback login method when the user forgets their password.
- Integration with social sign-in has improved, and it is now possible to use the email verified status from the social sign-in provider.
- Ory Elements and the default Ory Account Experience are now internationalized with translations.
- It is now possible to convert an Ory Session Cookie or Ory Session Token into a JSON Web Token.
- Recovery on native apps has improved significantly and no longer requires the user to switch to a browser for the recovery step.
- Administrators can now find users by their identifiers with fuzzy search - this feature is still in preview.
- Importing HMAC-hashed passwords is now possible.
- Webhooks can now update identity admin metadata.
- New screens have been added to make account linking possible when a user has registered with a password and later tries signing in with a social account sharing the same email.
- Ability to revoke all sessions of a user when they change their password.
- Webhooks are now available for all login, registration, and login methods, including Passkeys, TOTP, and others.
- The login screen now longer shows “ID” for the primary identifier, but instead extracts the correct label - for example, “Email” or “Username” from the Identity Schema.
- Login hints help users with guidance when they are unable to sign in (wrong social sign-in provider) but have an active account.
- Phone numbers can now be verified via an SMS gateway like Twilio.
- SMS OTP is now a two-factor option.
The following features have been shipped exclusively to Ory Network for this version:
- B2B SSO allows your customers to connect their LDAP / Okta / AD / … to your login. Ory selects the correct login provider based on the user’s email domain.
- Significantly better API performance for expensive API operations by specifying the desired consistency (
strong,eventual). - Finding users effortlessly with our new fuzzy search for credential identifiers available for the Identity List API.
Ory Kratos 1.1 is a major release that marks a significant milestone in our journey.
We sincerely hope that you find these new features and improvements in Ory Kratos 1.1 valuable for your projects. To experience the power of the latest release, we encourage you to get the latest version of Ory Kratos here or leverage Ory Kratos in Ory Network — the easiest, simplest, and most cost-effective way to run Ory.
For organizations seeking to upgrade their self-hosted solution, Ory offers enterprise support services to ensure a smooth transition. Our team is ready to assist you throughout the migration process, ensuring uninterrupted access to the latest features and improvements. Additionally, we provide various support plans specifically tailored for self-hosting organizations. These plans offer comprehensive assistance and guidance to optimize your Ory deployments and meet your unique requirements.
We extend our heartfelt gratitude to the vibrant and supportive Ory Community. Without your constant support, feedback, and contributions, reaching this significant milestone would not have been possible. As we continue on this journey, your feedback and suggestions are invaluable to us. Together, we are shaping the future of identity management and authentication in the digital landscape.
Contributors to this release in no particular order: moose115, K3das, sidartha, efesler, BrandonNoad ,Saancreed, jpogorzelski, dreksx, martinloesethjensen, cpoyatos1, misamu, tristankenney, nxy7, anhnmt
Are you passionate about security and want to make a meaningful impact in one of the biggest open-source communities? Join the Ory community and become a part of the new ID stack. Together, we are building the next generation of IAM solutions that empower organizations and individuals to secure their identities effectively.
Want to check out Ory Kratos yourself? Use these commands to get your Ory Kratos project running on the Ory Network:
brew install ory/tap/cli
scoop bucket add ory <https://github.com/ory/scoop.git>
scoop install ory
bash <(curl <https://raw.githubusercontent.com/ory/meta/master/install.sh>) -b . ory
sudo mv ./ory /usr/local/bin/
ory auth login
ory create project --name "My first Kratos project"
ory open account-experience registration
ory patch identity-config \
--replace '/identity/default_schema_id="preset://username"' \
--replace '/identity/schemas=[{"id":"preset://username","url":"preset://username"}]' \
--format yaml
ory open account-experience registration
Breaking Changes
Pagination parameters for the list identities CLI command have changed from arguments to flags --page-token and page-size:
- kratos list identities 1 100
+ kratos list identities --page-size 100 --page-token ...
Furthermore, the JSON / JSON pretty output of list identities has changed:
-[
- { "id": "..." },
- { /* ... */ },
- // ...
-]
...v1.0.0
We are thrilled to announce Ory Kratos v1.0, the powerful Identity, User Management, and Authentication system! With this major update, Ory Kratos brings a host of enhancements and fixes that greatly improve the user experience and overall performance.
Ory Kratos 1.0 is stable and robust
Several compelling reasons led to label Ory Kratos as a major release and graduated project: Ory Identities on Ory Network, powered by Ory Kratos, has been serving production traffic for well over a year, flawlessly. Ory Kratos is successfully processing over 100 million API requests daily and has about 100 million Docker Pulls. We have maintained stability within the Ory Kratos APIs for nearly two years, demonstrating their robustness and reliability. No breaking changes mean that developers can trust the stability of Ory Kratos in production.
Notable changes
Ory Kratos 1.0 introduces a variety of new features while focusing on stability, robustness, and improved performance. Major enhancements include support for social login and single-sign-on via OpenID connect in native apps, emails sent through HTTP rather than SMTP, and full compatibility with Ory Hydra v2.2.0. Users will also find multi-region support in the Ory Network for broader geographic reach, improved export functionality for all credential types, and enhanced session management with the introduction of the "provider ID" parameter. Other additions comprise distroless images for leaner resource utilization and faster deployment and support for the Lark OIDC provider.
New features and full multi-region support in Ory Network
Significant improvements and fixes accompany these new features. Enhanced OIDC flows now include the ability to forward prompt upstream parameters, offering developers increased flexibility and customization options. The logout flow also supports the return_to parameter, facilitating more flexible redirection post-user logout. Performance has been a key focus, with Ory Kratos 1.0 now capable of handling hundreds of millions of active users monthly. Critical bug fixes have been applied to prevent users from being redirected to incorrect destinations, ensuring smoother authentication and authorization. Additionally, there's more support for legacy systems via implemented crypt(3) hashers and a fix for metadata patching has been deployed to ensure consistent user metadata management. For a detailed view of all changes, refer to the changelog on GitHub. Feedback and support are, as always, greatly appreciated.
Support options for Ory Kratos 1.0
Ory Kratos 1.0 is a major release that marks a significant milestone in our journey.
We sincerely hope that you find these new features and improvements in Ory Kratos 1.0 valuable for your projects. To experience the power of the latest release, we encourage you to get the latest version of Ory Kratos here or leverage Kratos in Ory Network — the easiest, simplest, and most cost-effective way to run Ory.
For organizations seeking to upgrade their self-hosted solution, Ory offers dedicated support services to ensure a smooth transition. Our team is ready to assist you throughout the migration process, ensuring uninterrupted access to the latest features and improvements. Additionally, we provide various support plans specifically tailored for self-hosting organizations. These plans offer comprehensive assistance and guidance to optimize your Ory deployments and meet your unique requirements.
A Shoutout to the Ory Community
We extend our heartfelt gratitude to the vibrant and supportive Ory Community. Without your constant support, feedback, and contributions, reaching this significant milestone would not have been possible. As we continue on this journey, your feedback and suggestions are invaluable to us. Together, we are shaping the future of identity management and authentication in the digital landscape.
Contributors to this release in alphabetical order: borisroman, ci42, CNLHC, David-Wobrock, giautm, IchordeDionysos, indietyp, jossbnd, kralicky, PhakornKiong, sunakan, steverusso
Are you passionate about security and want to make a meaningful impact in one of the biggest open-source communities? Join the Ory community and become a part of the new ID stack. Together, we are building the next generation of IAM solutions that empower organizations and individuals to secure their identities effectively.
Give it a go
Want to check out Ory Kratos yourself? Use these commands to get your Ory Kratos project running on the Ory Network:
brew install ory/tap/cli
scoop bucket add ory https://github.com/ory/scoop.git
scoop install ory
bash <(curl <https://raw.githubusercontent.com/ory/meta/master/install.sh>) -b . ory
sudo mv ./ory /usr/local/bin/
ory auth
ory create project --name "My first Kratos project"
ory open account-experience registration
ory patch identity-config \\
--replace '/identity/default_schema_id="preset://username"' \\
--replace '/identity/schemas=[{"id":"preset://username","url":"preset://username"}]' \\
--format yaml
ory open account-experience registrationBug Fixes
-
Ability to patch metadata even if it is
null(#3304) (3c04d8f) -
Accept OIDC login request in browser+JSON login flow (#3271) (ad54093):
-
fix: OIDC login in browser JSON flow
-
test: add test for OIDC+JSON continuity cookie
-
-
Add error checking when creating verification code (#3328) (7182eca)
-
Add missing SessionIssued event for api flows (#3348) (adf78e0):
- fix: missing SessionIssued event for api flows
- chore: add SessionIssued event to post registration hook
- chore: format
- chore: move sessionissued event to persister
-
Cypress TOTP test (eac908c)
-
Don't assume the login challenge to be a UUID (#3317) (3172862):
For compatibility with ory/hydra#3515, which
now encodes the whole flow in the login challenge, we cannot further
assume that the challenge is a UUID. -
e2e: Install kratos-selfservice-ui-node peer deps (#3354) (ce20063)
-
Identity list pagination (#3325) (9d3ef0d):
Resolves a pesky issue that would skip the last page.
-
Properly normalize uppercase mail addresses (4984e0f):
-
Provide index hint in QueryForCredentials (#3329) (4ba530e):
-
fix: provide index hint in QueryForCredentials
-
feat: remove customizable join pr...
-
v0.13.0
We’re excited to announce the release of Ory Kratos v0.13.0! This update brings many enhancements and fixes, improving the user experience and overall performance. In general, Ory Kratos is reaching complete API stability and we're adding some missing features next, paving the road to v1.0.
Ory Kratos serves over 500M users monthly in various companies, and is the backbone of the Ory Network (the best, cheapest, easiest way to run Ory).
Here are the highlights:
- We’ve added new social sign-in options with Patreon OIDC and LinkedIn providers, making it even easier for your users to register and log in. Furthermore, we’ve introduced a new admin API that allows you to remove specific 2nd factor credentials, giving you more control over your user accounts.
- Performance has been a key focus in this release. We’ve optimized the whoami calls, parallelized the getIdentity and getSession calls, and made asynchronous webhooks fully async. These improvements will result in faster response times and a smoother experience for your users. Additionally, we’ve implemented better tracing to help you diagnose and resolve issues more effectively.
- We’ve also made several updates to the webhook system. A new response.parse configuration has been introduced, allowing you to update identity data during registration. This includes admin/public metadata, identity traits, enabling/disabling identity, and modifying verified/recovery addresses. Please note that can_interrupt is now deprecated in favor of response.parse.
- Lastly, we’ve made several important fixes, such as resolving the wrong message ID on resend code buttons, implementing the offline scope as Google expects, and improving the OIDC flow on duplicate account registration. We’ve also added the ability to configure whether the system should notify unknown recipients when attempting to recover an account or verify an address, enhancing security with “anti-account-enumeration measures.”
We hope you enjoy these new features and improvements in Ory Kratos v0.13.0! All features are already live on the Ory Network - the simplest, fastest and most scalable way to run Ory.
Please note that the v0.12.0 release was skipped due to CI issues.
Head over to the changelog at https://github.com/ory/kratos/blob/master/CHANGELOG.md to read all the details. As always, we appreciate your feedback and support!
Breaking Changes
By default, Kratos no longer sends out these Emails. If you want to keep notifying unknown addresses (keep the current behavior), set selfservice.flows.recovery.notify_unknown_recipients to true for recovery, or selfservice.flows.verification.notify_unknown_recipients for verification flows.
Bug Fixes
-
Account experience redirects to verification page (#3195) (2e96d75)
-
Account settings broken on OIDC removal (#3185) (61ae531), closes ory-corp/cloud#3514
-
Add
after_verification_return_toto sdk and api docs (#3097) (c70704c), closes #3096 -
Add
HydraLoginRequeston flow creation (#3152) (09312dd), closes #3108:The oauth2_login_request field was missing when initially creating the login flow.
-
Add missing
codediscriminator in updateVerificationFlow (#3213) (21576be) -
Add mutex to test SMTP server setup/teardown (20c2359)
-
Avoid unchecked casts from IdentityPool to PrivilegedIdentityPool (71d35dd)
-
Correctly apply patches to identity metadata (#3103) (1193a56), closes #2950
-
Don't return 500 if active strategy is disabled (#3197) (3a734c2)
-
Don't treat missing session as error in tracing (290d28a)
-
Error messages in OpenAPI/Swagger / improve error messages from failed webhooks and client timeouts (#3218) (b1bdcd3)
-
Handle upstream errors in patreon provider (#3032) (39fa31f)
-
Identity.CopyWithoutCredentials (989c99d)
-
Implement offline scope in the way google expects (#3088) (39043d4)
-
Improve webhook resilience (#3200) (0a05d99):
- fix: improve webhook logging
- chore: bump x
- feat: decouple context in PostRegistrationPostPersist hook
-
Invalid SQL syntax in ListIdentities (#3202) (162ab9b):
PostgresQL does not support
... WHERE x IN ( )with an empty argument list. -
Issuer missing from netid claims (#3080) (dec7cbc):
The NetID provider omits the issuer claim in the userinfo response. To resolve this issue, the ID token returned by NetID is now validated and its
subandissvalues are used. -
Lint errors and unused code (ae49ef0)
-
Make session AAL satisfaction check resilient against a nil identity in the session (5ab1a56):
Also fix tracing.
-
Nolint comment (93e6501)
-
Only return one result set for credentials_identifier (#3107) (59f35d1), closes #3105
-
Orphaned webhook spans (a7f9414)
-
Re-use existing CSRF token in verification flows (#3188) (08a3447):
-
fix: re-use existing CSRF token in verification flows
-
chore: fix if/else
-
-
Reduce SQL tracing noise (1650426)
-
Remove
http.Redirectfromshow_verification_uihook (#3238) (054705b) -
Report correct errors for json schema validation (#3085) (9477ea4):
- Implemented the translation of
jsonschema.ValidationErrorto errors codes documented here - Added missing error codes for relevant schema errors
Validation Name ID maxLengthEr...
- Implemented the translation of
v0.11.1
- Fixed several bugs to improve overall stability.
- Optimized performance for faster load times and smoother operation.
- Improved tracing capabilities for better debugging and issue resolution.
We are constantly working to improve Ory Kratos and this release is no exception. Thank you for using Ory and please let us know if you have any feedback or encounter any issues.
Breaking Changes
The /admin/courier/messages endpoint now uses keysetpagination instead.
Bug Fixes
-
Add missing indexes for identity delete (#2952) (dc311f9):
This significantly improves the performance of identity deletes.
-
Cors headers not added to the response #2922 (#2934) (1ed6839)
-
Flaky test now stable (4e5dcd0)
-
Pin geckodriver version to bypass GitHub API quota (#2972) (585cb9e)
-
Remove unused x-session-cookie parameter (#2983) (56b5c26):
This patch removes the undocumented and experimental
X-Session-Cookieheader from the/sessions/whoamiendpoint. -
Respect
return_toURL parameter in registration flow when the user is already registered (#2957) (3462ce1) -
Set config at the start (e58bc6e)
-
Spurious cancelation of async webhooks, better tracing (#2969) (72de640):
Previously, async webhooks (response.ignore=true) would be canceled
early once the incoming Kratos request was served and it's associated
context released. We now dissociate the cancellation of async hooks
from the normal request processing flow. -
TOTP internal context after saving settings (#2960) (8b647b1), closes #2680
-
Update pquerna/otp to fix TOTP URL encoding (#2951) (7248636):
v1.4.0 fixes generating TOTP URLs. Query params now use %20 instead of +
to encode spaces. + was not correctly interpreted by some Android
authenticator apps, and would show up in the issuer name, e.g. "My+Issuer"
instead of "My Issuer". -
Update year (d77e2cf)
-
Webhook tracing instrumentation+memory leak (f0044a3)
Code Generation
- Pin v0.11.1 release commit (41595c5)
Documentation
Features
-
Add client IP to span events (7ce3a74)
-
Improve error message when no session is found (#2988) (7ad2b97)
-
Remove duplicate queries from whoami calls (#2995) (b50a222), closes #2402:
Introduces an expand API to the identity persister which greatly improves whoami performance.
Tests
- Improve parallelization (e8e8ce5)
- Regenerate csrf if verification flow expired (#2455) (7025081)
- Update integrity snapshots (#3000) (6d26e5c)
Changelog
- 727439c autogen(docs): generate and bump docs
- b3b6f88 autogen(docs): regenerate and update changelog
- d8d47c9 autogen(docs): regenerate and update changelog
- ac05259 autogen(docs): regenerate and update changelog
- d8a2cbd autogen(docs): regenerate and update changelog
- a3096c7 autogen(docs): regenerate and update changelog
- e11ba52 autogen(docs): regenerate and update changelog
- 4e1d470 autogen(docs): regenerate and update changelog
- 0b109cd autogen(docs): regenerate and update changelog
- 97e9356 autogen(docs): regenerate and update changelog
- 5917258 autogen(docs): regenerate and update changelog
- d895a26 autogen(docs): regenerate and update changelog
- b6bd3f4 autogen(docs): regenerate and update changelog
- 8fbb1bb autogen(docs): regenerate and update changelog
- 8bb3f2a autogen(docs): regenerate and update changelog
- 83131fc autogen(docs): regenerate and update changelog
- 935d115 autogen(docs): regenerate and update changelog
- 94e01a9 autogen(docs): regenerate and update changelog
- c52425e autogen(docs): regenerate and update changelog
- 6fddfbf autogen(docs): regenerate and update changelog
- 03b3c29 autogen(docs): regenerate and update changelog
- 6134150 autogen(docs): regenerate and update changelog
- ce72501 autogen(openapi): regenerate swagger spec and internal client
- bef1a6c autogen: add v0.11.0 to version.schema.json
- 41595c5 autogen: pin v0.11.1 release commit
- 2f9b001 chore: add missing security annotations to admin handlers (#2937)
- 561e568 chore: cleanup test (#2964)
- 20da533 chore: pin nancy (#2977)
- 131b8c5 chore: update repository templates to ory/meta@a1264fa
- ab1abee ci: fix dockle action
- fc2787b docs: improve api headline (#2989)
- b407aa9 feat: add NID to logs in courier (#2956)
- 7ce3a74 feat: add client IP to span events
- 7ad2b97 feat: improve error message when no session is found (#2988)
- 04d0280 feat: improve tracing (#2992)
- b50a222 feat: remove duplicate queries from whoami calls (#2995)
- efb8ae8 feat: require verification on login (#2927)
- fc7aa86 feat: store errors of courier message (#2914)
- 8b647b1 fix: TOTP internal context after saving settings (#2960)
- bbb3995 fix: add missing indexes (#2973)
- dc311f9 fix: add missing indexes for identity delete (#2952)
- 1ed6839 fix: cors headers not added to the response #2922 (#2934)
- ae8ad7b fix: dont reset to false (#2965)
- 4e5dcd0 fix: flaky test now stable
- 3e06c99 fix: listing sessions query (#2958)
- 3b50711 fix: missing index on courier list count (#3002)
- 585cb9e fix: pin geckodriver version to bypass GitHub API quota (#2972)
- a7720b2 fix: quickstart demos (#2940)
- 33b01bb fix: remove duplicate query in GetIdentity (#2987)
- 56b5c26 fix: remove unused x-session-cookie parameter (#2983)
- ca35b45 fix: resilient social sign in (#3011)
- 3462ce1 fix: respect
return_toURL parameter in registration flow when the user is already re...
v0.11.0
The 2022 winter release of Ory Kratos is here, and we are extremely excited to share with you some of the highlights included:
- Ory Kratos now supports verification and recovery codes, which replace are now the default strategy and should be used instead of magic links.
- Import of MD5-hashed passwords is now supported.
- Ory Kratos can now act as the login app for the Ory Hydra Consent & Login Flow using the
oauth2_provider.urlconfiguration value. - Ory Kratos' SDK is now released as version 1. Learn more in the upgrade guide.
- New APIs are available to manage Ory Sessions.
- Ory Sessions now contain device information.
- Added all claims to the Social Sign-In data mapper as well as the option to customize admin and public metadata.
- Add webhooks that can block the request, useful to do some additional validation.
- Add asynchronous webhooks which do not block the request.
- A CLI helper to clean up stale data.
Please read the changelog carefully to identify changes which might affect you. Always test upgrading with a copy of your production system before applying the upgrade in production.
Breaking Changes
This patch changes the behavior of the recovery flow. It introduces a new strategy for account recovery that sends out short "one-time passwords" (code) that a user can use to prove ownership of their account and recovery access to it. This PR also updates the default recovery strategy to code.
This patch invalidates recovery flows initiated using the Admin API. Please re-generate any admin-generated recovery flows and tokens.
This is a breaking change, as it removes the courier.message_ttl config key and replaces it with a counter courier.message_retries.
SDK Method getJsonSchema was renamed to getIdentitySchema.
Bug Fixes
-
Active attribute based off IsActive checks (#2901) (bcbf68e)
-
Add issuerURL for apple id (#2565) (2aeb0a2):
No issuer url was specified when using the Apple ID provider,
this forced usersers to manually enter it in the provider config.This PR adds the Apple ID issuer url to the provider simplifying the setup.
-
Add missing go.mod to docker build (7c4964e)
-
Add support for verified Graph API calls for facebook oidc provider (#2547) (1ba7c66)
-
Admin recovery CSRF & duplicate form elements (#2846) (de80b7f)
-
Bump graceful to deal with http header timeouts (9ce2d26)
-
Check return code of ms graphapi /me request. (#2647) (3f490a3)
-
Correct name of span on recovery code deletion (#2823) (44f775f)
-
Correctly calculate
expired_attimestamp for FlowExpired errors (#2836) (ddde43e) -
Disappearing title label on verification and recovery flow (#2613) (29aa3b6), closes #2591
-
Distinguish credential types properly when collecting identifiers (#2873) (705f7b1)
-
Do not crash process on invalid smtp url (#2890) (c5d3ebc):
Closes ory-corp/cloud#3321
-
Do not double-commit webhooks on registration (#2888) (88e75d9)
-
docker: Update images (b5f80c1)
-
Express e2e tests for new account experience (#2708) (84ea0cf)
-
Format (0934def)
-
Gosec false positives (e3e7ed0)
-
Identity sessions list response includes pagination headers (#2763) (0c2efa2), closes #2762
-
identity: Migrate identity_addresses to lower case (#2517) (c058e23), closes #2426
-
Ignore commata in HIBP response (0856bd7)
-
Ignore CSRF for session extension on public route (866b472)
-
Ignore error explicitly (772d596)
-
Include flow id in use recovery token query (#2679) (d56586b):
This PR adds the
selfservice_recovery_flow_idto the query used when "using" a token in the recovery flow.This PR also adds a new enum field for
identity_recovery_tokensto distinguish the two flows: admin versus self-service recovery. -
Include metadata_admin in admin identity list response (#2791) (aa698e0), closes #2711
-
Incorrect swagger annotation for
getSession(#2891) (797ea68) -
lint: Fixed lint error causing ci failures (4aab5e0)
-
Make hydra consistently localhost (70211a1)
-
Make ID field in VerifiableAddress struct optional (#2507) (0844b47), closes #2506
-
Make servicelocator explicit (4f841da)
-
Make swagger/openapi go 1.19 compatible (fec6772)
-
Mark gosec false positives (13eaddb)
-
Metadata should not be required ([05afd68](05afd68381abe58c5e7cdd51cb...
v0.10.1
Re-release the SDK.
Bug Fixes
- Bump ory cli (12ceae0)
Code Generation
- Pin v0.10.1 release commit (ab16580)
Changelog
- 290dbd7 autogen(docs): generate and bump docs
- 0290986 autogen(docs): regenerate and update changelog
- fb2ddf3 autogen(docs): regenerate and update changelog
- 94c620d autogen: add v0.10.0 to version.schema.json
- ab16580 autogen: pin v0.10.1 release commit
- 12ceae0 fix: bump ory cli
Artifacts can be verified with cosign using this public key.
v0.10.0
We achieved a major milestone - Ory Kratos is out of alpha! Ory Kratos had no major changes in the APIs for the last months and feel confident that no large breaking changes will need to be introduced in the near future.
This release focuses on quality-of-live improvements, resolves several bugs, irons out developer experience issues, and introduces session renew capabilities!
Breaking Changes
Please be aware that the SDK method signatures for submitSelfServiceRecoveryFlow, submitSelfServiceRegistrationFlow, submitSelfServiceLoginFlow, submitSelfServiceSettingsFlow, submitSelfServiceVerificationFlow might have changed in your SDK.
This patch moves several CLI command to comply with the Ory CLI command structure:
- ory identities get ...
+ ory get identity ...
- ory identities delete ...
+ ory delete identity ...
- ory identities import ...
+ ory import identity ...
- ory identities list ...
+ ory list identities ...
- ory identities validate ...
+ ory validate identity ...
- ory jsonnet format ...
+ ory format jsonnet ...
- ory jsonnet lint ...
+ ory lint jsonnet ...This patch moves several CLI command to comply with the Ory CLI command structure:
- ory identities get ...
+ ory get identity ...
- ory identities delete ...
+ ory delete identity ...
- ory identities import ...
+ ory import identity ...
- ory identities list ...
+ ory list identities ...
- ory identities validate ...
+ ory validate identity ...
- ory jsonnet format ...
+ ory format jsonnet ...
- ory jsonnet lint ...
+ ory lint jsonnet ...Bug Fixes
-
Add flow id when return_to is passed to the verification (#2482) (c2b1c23)
-
Add indices for slow queries (e0cdbc9)
-
auth0: Created_at workaround (#2492) (52a965d), closes #2485
-
Avoid excessive memory allocations in HIBP cache (#2389) (ee2d410), closes #2354
-
Change SQLite database mode to 0600 (#2344) (0e5d3b7):
The default mode is 0644, which is allows broader access than necessary.
-
Correct location (b249aaa)
-
Do not expose debug in a response when a schema is not found (#2348) (aee2b1e)
-
Do not fail release if no changes needed (114c93e)
-
Dockerfile: Use existing builder base image (#2390) (37de25a)
-
Embed schema (b797bba)
-
Get user first name and last name from Apple (#2331) (4779909)
-
Improve error reporting from OpenAPI (8a1009b)
-
Improve performance of identity schema call (af28de2)
-
Internal Server Error on Empty PUT /identities/id body (#2417) (5a50231)
-
Load return_to and append to errors (#2333) (5efe4a3), closes #2275 #2279 #2285
-
Make delete formattable (0005f35)
-
New issue templates (b9ad684)
-
Refresh is always false when session exists (d3436d7), closes #2341
-
Remove wrong templates (4fe2d25)
-
Reorder transactions (78ca4c6)
-
Resolve index naming issues (d5550b5)
-
Resolve MySQL index issues (50bdba9)
-
Resolve otelx panics (6613a02)
-
sdk: Improved OpenAPI specifications for UI nodes (#2375) (a42a0f7), closes #2357
-
Serve.admin.request_log.disable_for_health behaviour (#2399) (0a381fa)
-
sql: Add additional join argument to resolve MySQL query issue (854e5cb), closes #2262
-
Use
pathinstead offilepathto join http route paths (16b1244), closes #2292 -
Use JOIN instead of iterative queries (0998cfb), closes #2402
-
Use pointer of string for PasswordIdentifier in example code (#2421) (61f12e7)
-
Use predictable SQLite in memory DSNs (#2415) (51a13f7), closes #2059
Code Generation
- Pin v0.10.0 release commit (87e0de7)
Code Refactoring
- Deprecate fizz renderer (5277668)
- Move CLI commands to match Ory CLI structure (d11a9a9)
- Move CLI commands to match Ory CLI structure (73910a3)
Documentation
- Add docs about change in default schema (#2447) (5093cd4)
- Remove notice importing credentials not possible (#2418) (b80ed69)