ObjectivePGP is an implementation of OpenPGP protocol for iOS and macOS. OpenPGP is the most widely used email encryption standard. It is defined by the OpenPGP Working Group of the Internet Engineering Task Force (IETF).
Here is the blog post story.
You are welcome to contribute. Please create Pull Request against develop branch.
#import <ObjectivePGP/ObjectivePGP.h>import ObjectivePGPNSArray<PGPKey *> *keys = [ObjectivePGP readKeysFromPath:@"/path/to/key.asc" error:nil];let keys = try ObjectivePGP.readKeys(fromPath: "/path/to/key.asc")Keyring is a storage (in memory or on disk) that keep all sorts of PGP keys.
PGPKeyring *keyring = ObjectivePGP.defaultKeyring;
PGPKeyring *keyring = [[PGPKeyring alloc] init];
NSArray<PGPKey *> *allKeys = keyring.keys;
[keyring importKeys:@[key]];
[keyring deleteKeys:@[key]];
[keyring importKey:@"979E4B03DFFE30C6" fromPath:@"/path/to/secring.gpg"];
PGPKey *key = [keyring findKeyWithIdentifier:@"979E4B03DFFE30C6"];
NSArray<PGPKey *> keys = [pgp findKeysForUserID:@"Name <[email protected]>"];let keyring = ObjectivePGP.defaultKeyring
let keyring = Keyring()
let allKeys = keyring.keys
keyring.import(keys: [key])
keyring.delete(keys: [key])
keyring.import(keyIdentifier:"979E4B03DFFE30C6", fromPath:"/path/to/secring.gpg")
if let key = keyring.findKey("979E4B03DFFE30C6") {
// key found in keyring
}
keyring.findKeys("Name <[email protected]>").forEach(key) {
// process key
}// Write keyring to file
[[keyring export:error] writeToURL:[NSURL fileURLWithString:@"keyring.gpg"]];
// Public keys data
NSData *publicKeys = [keyring exportKeysOfType:PGPKeyTypePublic error:nil];// Write keyring to file
try keyring.export().write(to: URL(fileURLWithPath: "keyring.gpg"))
// Public keys (Data)
let publicKeys = keyring.exportKeys(of: .public)Sign a data with a key:
NSData *signature = [ObjectivePGP sign:fileContent detached:YES usingKeys:@[key] passphraseForKey:nil error:nil];
[ObjectivePGP verify:fileContent withSignature:signature usingKeys:@[key] passphraseForKey:nil error:nil];let signature = try ObjectivePGP.sign(encryptedBin, detached:true, using: [key1])
try ObjectivePGP.verify(encryptedBin, withSignature: signature, using: [key1])NSData *encrypted = [ObjectivePGP encrypt:fileContent addSignature:YES usingKeys:@[key] passphraseForKey:nil error:nil];
[ObjectivePGP decrypt:encrypted andVerifySignature:YES usingKeys:@[key] passphraseForKey:nil error:nil];let encrypted = try ObjectivePGP.encrypt(fileContent), addSignature: true, using: [key1, key2])
let decrypted = try ObjectivePGP.decrypt(encrypted, andVerifySignature: true, using: [key1])PGPKeyGenerator *generator = [[PGPKeyGenerator alloc] init];
PGPKey *key = [generator generateFor:@"Marcin <[email protected]>" passphrase:nil];
NSData *publicKeyData = [key export:PGPKeyTypePublic error:nil];
NSData *secretKeyData = [key export:PGPKeyTypeSecret error:nil];let key = KeyGenerator().generate(for: "[email protected]", passphrase: "password")
let publicKey = try key.export(keyType: .public)
let secretKey = try key.export(keyType: .secret)ASCII armor is a binary-to-textual encoding converter. ASCII armor involves encasing encrypted messaging in ASCII so that they can be sent in a standard messaging format such as email.
Example:
-----BEGIN PGP PUBLIC KEY BLOCK-----
Comment: For info see http://www.objectivepgp.org
[...]
-----END PGP PUBLIC KEY BLOCK-----
Class PGPArmor can be used to convert binary format to ASCII format
NSString *armoredKey = [PGPArmor armoredData:encrypted as:PGPArmorPublicKey];let armoredKey = Armor.armored(Data(), as: .publicKey)When convert manually, it is important to use right PGPArmorType value that define the header. It may be a tricky part so here's the cheatsheet:
| Type data | PGPArmorType | Example |
|---|---|---|
| Encrypted | PGPArmorMessage |
Armor.armored(ObjectivePGP.encrypt(...), as: .message) |
| Decrypted | PGPArmorMessage |
Armor.armored(ObjectivePGP.decrypt(...), as: .message) |
| Pubic key | PGPArmorTypePublic |
Armor.armored(key.export(), as: .publicKey) |
| Secret key | PGPArmorTypeSecret |
Armor.armored(key.export(), as: .secretKey) |
For any result of encryption the type is PGPArmorMessage
target 'TargetName' do
use_frameworks!
pod 'ObjectivePGP'
endObjectivePGP comes with the Frameworks for the latest release.
- Download latest ObjectivePGP.framework or build a framework with the build-frameworks.sh script.
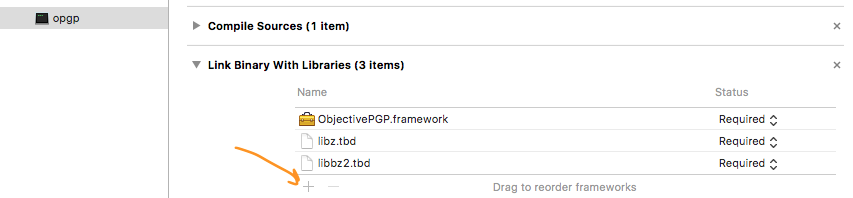
- Link framework with the target
- Link libraries and frameworks
- Add
Security.frameworkto "Link Binary With Libraries" list for the target. These are system libraries. - Add
libzandlibbz2to "Link Binary With Libraries" list for the target. These are system libraries.
- Add
- In the Build Phases tab, click the + button at the top and select “New Run Script Phase”. Enter the following code into the script text field:
bash "${BUILT_PRODUCTS_DIR}/${FRAMEWORKS_FOLDER_PATH}/ObjectivePGP.framework/strip-frameworks.sh"(The last step, is required for working around an iOS App Store bug when archiving universal binaries.)
See CHANGELOG
Known limitations:
- Elgamal cipher is not supported.
- Cleartext signature.
The ObjectivePGP stays under a dual license:
-
Free for non-commercial use, covered by the standard 2-clause BSD license. That means you have to mention Marcin Krzyżanowski as the original author of this code and reproduce the LICENSE text inside your app.
-
Commercial-use license to use in commercial products. Please bear in mind that some free products remain commercial products. Please contact me via email for details.
Not sure what to choose? check this thread
This product uses software developed by the OpenSSL Project for use in the OpenSSL Toolkit. (http://www.openssl.org/)